- Vulnerable U
- Posts
- 🎓 VulnU #016: The Power of Empathy in Infosec
🎓 VulnU #016: The Power of Empathy in Infosec
5 Key Steps to a Stronger Defense
Read Time: 7 minutes

Howdy friends! -
Writing this one from home in ATX where I just wrapped recording an episode of Decipher Security’s podcast with DennisF over at Duo. We talked breaking into infosec, trends I’m seeing in cloud security, and my mission here at Vulnerable U. I’ll link it when that episode drops!
Today, we delve into the power of empathy and how it can enhance our defenses and improve our security posture along with just being better people in general.
Also, for subscribers who are friends and family (or any other subscribers interested to know), this week was the anniversary of this pup crossing over the rainbow bridge. Miss her everyday.
 Lola in curiosity mode. | Lola in the wild.  |
Any of you reading this who used to hang around the Houston infosec scene might’ve met my giant dogs. Lola was the best and I brought her everywhere with me back then.
Let’s Get Vulnerable
I’ve talked about different overlooked superpowers in infosec before, and I think another one of them is empathy.
Cultivating empathy allows us to step into the shoes of others, gaining valuable insights into their perspectives and experiences.
By fostering empathy within the infosec community, we can not only be better people, but we can build more effective and stronger defenses as a result.
Lets explore.
1️⃣ Understanding Threat Actors
One key skill in any relationship I’ve been in is learning how to fight well. This includes actually hearing each other out in the heat of the moment.
The same skill used here, empathy, can help us develop a deeper understanding of our threat actors’ motivations. Instead of thinking of them as faceless adversaries and a pile of IOCs, we can analyze their tactics, techniques, and procedures (TTPs) through a human lens.
By truly comprehending the underlying factors that drive hackers, such as financial gain or ideological motivations, we can better anticipate their actions and bolster our defenses and threat models accordingly.
As we learned last week’s newsletter, through analyzing the Verizon DBIR we’re finding that motivations are mostly financial.
Ways hackers will exploit for financial gain:
Stealing Direct Financial Information - banking credentials, insider info for stock trade advantages, etc.
Social Engineering - convincing victims to transfer money to them in one way or another.
Ransom and Digital Extortion - either via ransomware or by demanding ransom from victims of a data breach.
Online Blackmail - with this type of extortion there is a threat of revealing private information if demands are not met.
Knowing these things helps us plan against future attacks. What that plan looks like varies by company and potential threats based on your particular threat model.
2️⃣ Designing User-Centric Security
When it comes to protecting individuals and organizations, empathy allows us to prioritize user experience and build security measures that consider the human element.
By understanding the challenges and limitations faced by users, we can design intuitive security solutions that don't impede productivity or create unnecessary friction.
Empathy-driven security practices enable us to strike the right balance between usability, introducing friction, and robust protection.
Here are some examples of design done well (both user needs and security needs are met):
Your security tooling is integrated into developers pipeline and gives real time feedback and guardrails en route to production
Users are allowed to use a modern suite of productivity tools as you’ve built security controls in and around them
Zero Trust architectures which allow users to not constantly battle being onsite or on VPN to perform their job.
Apple’s “use the token you just got via SMS” feature
The “remember this device for 30 days” features of MFA challenges
Here are some examples of when design impeded usability:
Security team just tosses reports over the wall to developers with an SLA of when things need to be fixed
Policies that limit use of any and all modern productivity apps because the security team only has controls over Office 2007
Ever apply for a mortgage? Talk about a user story nightmare.
Gating every code change to production via a security code review before it is allowed to be merged.
3️⃣ Supporting Victims
In the aftermath of a cyberattack, empathy plays a vital role in supporting victims. Cyber incidents can have a ton of emotional, financial, and psychological effects, leaving individuals feeling violated and vulnerable.
By offering empathetic support, whether through clear communication, guidance, or access to resources, we can help victims navigate the aftermath of an attack and regain a sense of security.

Empathy fosters trust and empowers individuals to seek the assistance they need.
It also does one key thing that I like to talk about a lot here - encourage more victims to share the details of a breach so we can all learn from it. If everyone was getting hacked in silence, we’d have no idea what to protect ourselves from.
4️⃣ Human-Centric Training and Awareness
Empathy should extend to the realm of cybersecurity training and awareness programs. Recognizing that not everyone possesses the same level of technical expertise or awareness, empathy-driven education initiatives can bridge the knowledge gap.
By delivering training in a relatable and accessible manner, we empower individuals from all backgrounds to adopt safer online practices, ultimately strengthening the collective security posture.
5️⃣ Promoting Collaboration and Cooperation
This one I’ve talked about a lot. Embracing empathy encourages collaboration within the infosec community. By fostering an environment where professionals can share experiences, insights, and best practices openly, we create a collective defense ecosystem.
Empathy enables us to understand each other's challenges, celebrate successes, and work together towards a common goal of community resilience and enhanced cybersecurity.
Signing Off
Remember, empathy allows us to gain a comprehensive understanding of the human aspects involved, leading to more effective prevention and response strategies.
Let’s embrace empathy as a powerful tool in our defense arsenal. By putting ourselves in the shoes of others, we can forge stronger connections, understand motivations, and ultimately build a more resilient and empathetic infosec community. If you want more on empathy, check out this awesome podcast:
(A lot of friends have been on this show but you’ll notice a previous Community Spotlight of mine, InfosecSherpa was on one recently: here)
Elective Reading
It seems the Energy Department was “one of several” federal agencies dealing with the MOVEit breach we discussed last week.
Been keeping an eye on the regulation around TikTok, not because of my affinity for the social network itself, but because of the ripple effects this sort of legislation will have across the tech world.
What does it mean for a given state to ban a particular app? How is this even enforceable? Where will the lines in the sand be drawn?
“Hot on the heels of the recent emergency Google Chrome security update addressing a zero-day exploit, already seen in the wild, comes another critical Chrome browser security update. This one lists four vulnerabilities as being included, one of which is a critical issue in the browser ‘autofill payments’ function which automatically enters payment details in online forms.”
Let’s talk about Fortinet for a moment. Talk about a rough vuln to tackle. Updating software is hard enough, never mind managing a fleet of firmware upgrades for your network gear.
🚨 Over 250,000 Fortinet firewalls publicly accessible on the Internet.
They just dropped a patch for a major Remote Code Execution vulnerability.
...and then announced the vuln may have been used in attacks already.
Lets dive in 👇
— Matt Johansen (@mattjay)
Jun 13, 2023
The Shodan numbers aren’t great on this. This is a very easily exploitable bug and hundreds of thousands of these things are on the internet. This is also a bug ripe for Chinese threat actor groups who are targeting critical infrastructure sites, like the one we talked about a few weeks back attacking Guam.
It was a week of hardware security issues. Fortinet wasn’t the only pizza box on the network that needs updating. And actually, this Barracuda issue might not be fixable without trashing the device and replacing it.
That not bad enough for you? Well Mandiant has seen the bug exploited globally this week:
For those of you into malware, this is a really good writeup about “Fully Undetectable Malware” from TrendMicro: Read PDF here
“We uncovered hundreds of heavily obfuscated batch files for deploying both modified and fully undetectable (FUD) malware with the evolving BatCloak obfuscation engine. The vast majority of these samples gathered since 2022 are capable of persistently evading antivirus detection, granting threat actors the ability to load numerous malware families and exploits with ease through highly obfuscated batch files. As a matter of fact, 80% of the samples we’ve unearthed have no-detection across all security vendors.”

Staying on the malware topic - read this great run through of the Vidar infostealer malware campaign by Team Cymru.
The intention of this blog post is to provide a comprehensive update on how Vidar is administered / operated today.
Key Findings
- Vidar threat actors continue to rotate their backend IP infrastructure, favoring providers in Moldova and Russia.
- Evidence suggests that since our last blog post, the threat actors have taken steps to anonymize their activities using public VPN services.
- By tracking the hosting of the main Vidar site (presently my-odin[.]com), we are able to monitor other aspects of the threat actors infrastructure, potentially illuminating both affiliates and victims.
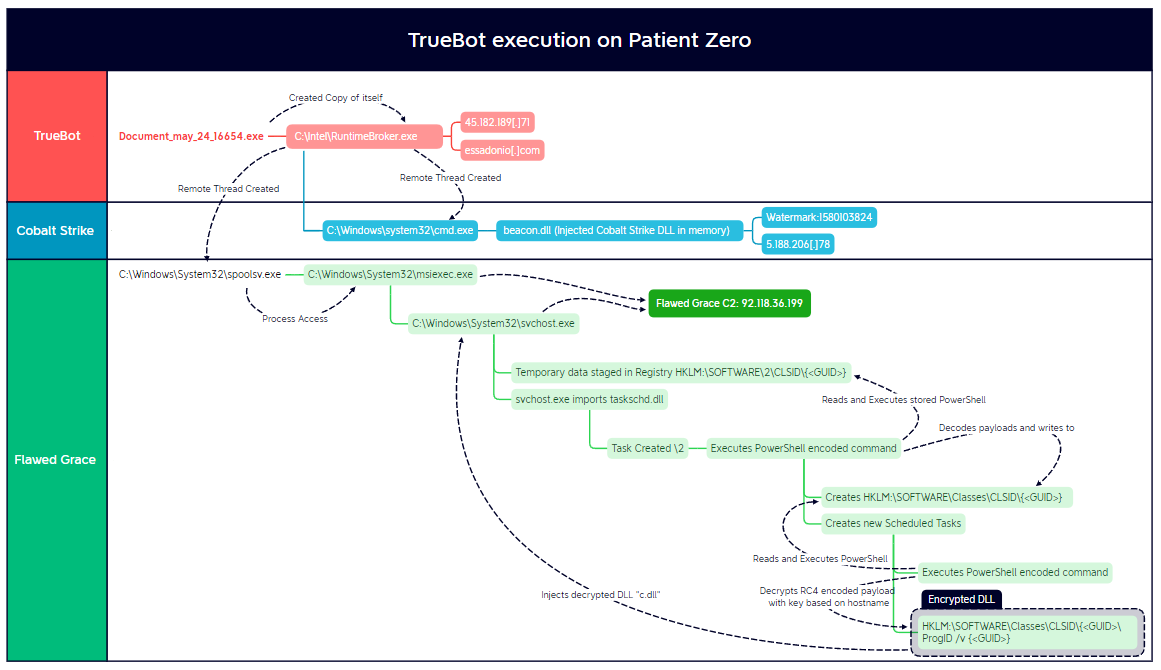
Incredible write up of an attack. Not only is a destructive attack like this rare, it’s even more rare to get a full run through like this.
Extra Credit
Help Us Grow! If you know someone who might be interested in joining the Vulnerable U community, please share this newsletter with them! As of now, spread will just be by word of mouth.
Parting Thoughts:
Let me know how I can help as always, if there's a topic you'd like to see covered in a future edition of the newsletter, or if you have any questions or concerns, please don't hesitate to reach out to us. I’m always happy to hear from our readers and help in any way I can.
Stay safe, Matt Johansen
@mattjay